NetOps + SecOps: The New Collaboration Model

 The divide between NetOps and SecOps teams was once thought to be necessary and unavoidable, with the former focusing their time and attention on network uptime, performance, and reliability, while the latter kept a close eye on cybersecurity threats, data breaches, and indicators of compromise (IoC).
The divide between NetOps and SecOps teams was once thought to be necessary and unavoidable, with the former focusing their time and attention on network uptime, performance, and reliability, while the latter kept a close eye on cybersecurity threats, data breaches, and indicators of compromise (IoC).
For decades, these siloed teams leveraged similar data sets but operated in isolation. Much like detectives unknowingly investigating the same crime scene, the two teams worked separately, focusing on their own clues without ever noticing the opportunities for collaboration that were hidden in plain sight.
The advent of NetSecOps is changing the equation once and for all.
What is NetSecOps?
As the name implies, the NetSecOps concept originated based on the logical integration of network operations (NetOps) and security operations (SecOps) to leverage common data sources and economies of scale. Experts with experience and insight into both realms realized the inherent impact of security issues on performance (and vice versa) that increasingly made siloed models inefficient.
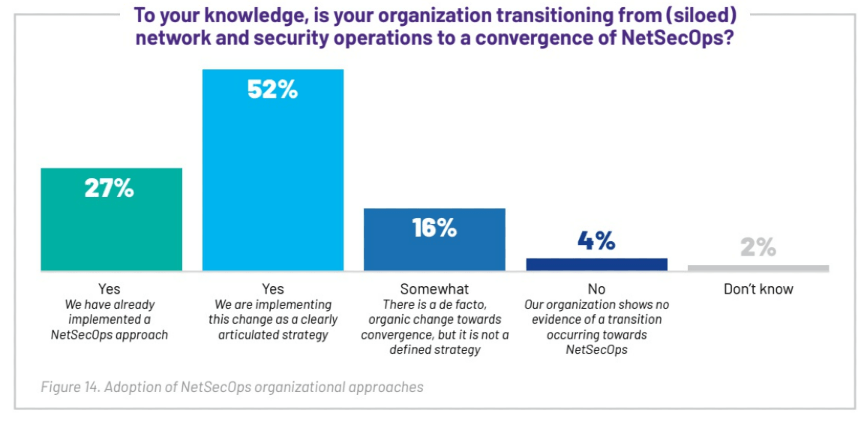
While this concept has existed for over a decade, the rise of hybrid and multi-cloud architecture, along with shifting network boundaries stimulated by a remote workforce, have accelerated the adoption of the NetSecOps model in recent years. The VIAVI 2025/26 State of the Network Study results reflect this trend, with 79% of organizations indicating they are now on the path to NetSecOps implementation or have already completed it.
Why NetSecOps is Important
NetSecOps isn’t just the latest industry buzzword – it’s a strategic convergence of two critical disciplines. Beyond the convenient sharing of information, this practice reduces costs by eliminating redundant tools, and removes IT resource constraints in an age of shrinking budgets and ongoing skilled labor challenges. This joining of forces also introduces valuable cross-training opportunities, as seasoned professionals on both sides of the equation approach retirement.
Along with these fundamental benefits driving the industry toward the NetSecOps model, organizations around the world also list faster issue resolution, threat mitigation, and end-to-end visibility among the motivating factors. Many of these proactive companies are looking ahead to the eventual challenges of IoT device proliferation at the network edge, and the application of next-level AI technology and machine learning (ML) algorithms to a common platform and data set.
Packets as a shared source of network truth
Of all the available network data sources, packets offer the most common benefits to both NetOps and SecOps, with the unabridged data providing an index to see who was communicating on the network at any point in time, identify potentially malicious traffic patterns, or point to the specific server, application, client, or network link responsible for bottlenecks and degradations in performance. In each scenario, having a back-in-time visibility afforded by packet capture also provides an ultimate source of truth for forensic investigations.
Whether an issue is security or performance related (or both), efficient root cause identification is essential for maintaining compliance, reliability, and customer trust in today’s IT ecosystem. Organizations with robust packet capture capabilities resolve incidents 44% faster, signaling the value of advanced packet capture and analysis and customizable workflows as unifying elements for emerging NetSecOps teams. This convergence also allows resources to be allocated logically as risks are assessed on an apples-to-apples basis.
Additional Tools of the NetSecOps Lifecycle
Packet capture and analysis is just one important element of the NetSecOps model. Additional data sources, monitoring tools, and workflows ensure complementary security and performance objectives are met and resources are utilized efficiently.
- Enriched flow data
Enriched flow records combine traditional flow data with user ID, syslog, and simple network management protocol (SNMP) information to form a structured and concise record with valuable insight into connectivity, traffic control, and usage patterns. NetSecOps teams leverage this treasure trove of data to enhance their threat detection, incident response, and forensic analysis capabilities.
- Metrics
NetOps and SecOps have traditionally monitored metrics like throughput, latency, dwell time, or threat detection rates geared toward their specific disciplines. To bridge the gap effectively, common metrics and KPIs like incident response times, mean time to resolve (MTTR), and mean time to detect (MTTD) help to prioritize NetSecOps activities while enhancing collaboration and accountability.
- Metadata
Metadata is free of the payload volume and accompanying storage requirements of full packet capture, but retains the critical context needed to detect and analyze both security and operational issues, even when traffic is encrypted. Rich metadata acts as a “detective’s notebook”, filled with useful clues about every packet and flow that passes through the network.
VIAVI Observer is the Ideal NetSecOps Solution
For NetSecOps teams to be successful, a common, scalable platform for network monitoring and security operations is essential. The VIAVI Observer Platform combines advanced threat intelligence powered by CrowdStrike®, high-fidelity forensic evidence and packet analysis, and proprietary VIAVI enriched flow and metadata in one dynamic solution.
Backed by advanced performance analytics and patented machine learning algorithms, Observer meets the challenges of NetSecOps teams head-on, offering an intuitive end-user experience (EUE) score for every transaction and on-demand application dependency mapping for immediate and intuitive multi-tier visibility. Purpose-built appliances and cloud-based options provide deployment flexibility, while user-friendly workflows quickly adapt to the needs and interests of each stakeholder.
The shift to NetSecOps is not about adding more tools—it’s about unlocking more value from the data you already rely on. When network and security teams operate from the same platform, with shared insight and evidence, investigations become clearer, decisions become faster, and outcomes become more predictable. The question is no longer whether convergence is needed, but how quickly your organization can take advantage of it.