The challenge of access security tackled with SAML solutions
Security Assertion Markup Language (SAML) solutions have the potential to greatly improve the overall security of an enterprise’s data, by enhancing the security which an employee gains access to the data and/or a service.
We can see today, that a vast majority of enterprises enable their employees with tools or services which are both internal e.g. email and external to the enterprise e.g. cloud based services – customer relationship management (CRM), file sharing, etc. For the enterprise the clear advantage of adopting SAML is simple; they gain greater security control over how employees access these unique services.
Why the need for SAML?
A simple and well known fact of modern security is that it is as strong as the weakest password, which tends to be extremely vulnerable. Which in turn weakens an enterprise ability to keep data secure. Another problematic or exposure point for enterprises is where an employee leaves the enterprise and the IT administrator forgets to de-activate that user for the external service.
The concept of SAML is to improve access security but to also simplify the management of potentially thousands of unique employees accessing multiple services. SAML uses a single trusted authentication or single sign-on mechanism, for which the enterprise can easily manage.
The basics behind SAML
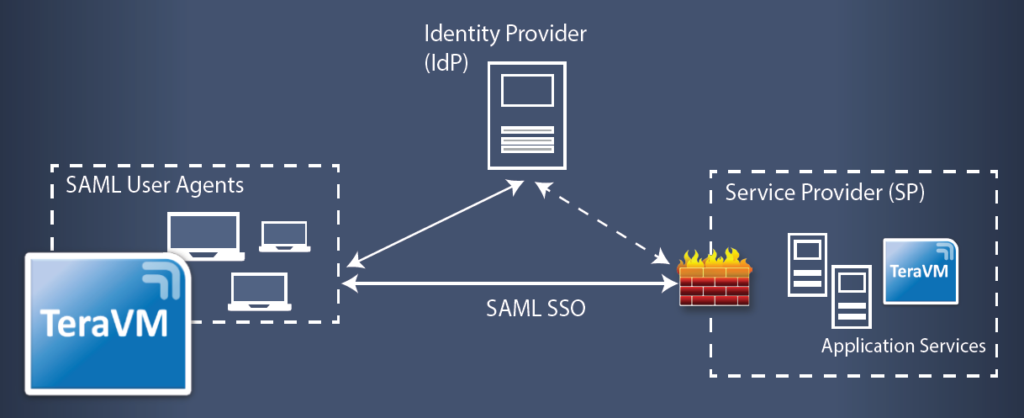
SAML is made up of a three way communication between the client i.e. you and I in front of our web-browser, a service provider e.g. a leading CRM service provider and an Identity provider (a trusted 3rd party service). When you and I as the client attempt to access the CRM solution, our browser gets redirected to the Identity provider (IdP), which for many of us is a transparent transaction.
The IdP then authenticates us as a valid user with the enterprise. The IdP assigns us with a security token, which authorizes access. The IdP then sends us back on our way to the service provider (SP), again all this is transparent to us (Note: If you look carefully at the address bar in the browser you may notice it iterate automatically through a number of URI). Once the service provider validates the security token with the identity provider, only then do we gain access to the data we originally requested on the CRM.
The advantage for you and I as consumers of SAML, is the ability to seamlessly switch between the different cloud services without the need to continuously enter user-names and passwords!
The SAML challenge
The challenge that many enterprises face today with SAML, is that there is no single industry standard and that solution vendors can provide unique approaches to their SAML 2.0 implementations. So for the solution vendor the challenge is to prove interoperability, but for the enterprise, the challenge is even more cumbersome as they need to validate the robustness and reliability of the identity provider and indeed the service provider’s implementation of SAML, proving that the elected solution is robust, reliable and can indeed scale to potentially millions of clients with unique user credentials.
Validation for SAML
Using TeraVM, users can emulate the most realistic load scenarios for performance validation of throughput, connections and latency for single sign-on services of SAML 2.0. TeraVM supports validation of SAML by emulating SAML clients compatible with the leading vendor’s of SAML solutions. TeraVM enables interoperability and validation of reliability for both Identity Provider (IdP) and Service Provider (SP) SAML solutions.
TeraVM statefully emulates SAML requests and responses as per a real world browser. This means that TeraVM can validate the authentication flow processes originating at either the IdP or SP. Furthermore, TeraVM’s per flow architecture means it can represent millions of unique client-side browsers (each one with unique credentials), enabling TeraVM to represent real world validation scenarios for SAML at scale.
In addition, TeraVM’s per flow capability means it is used to validate reliability SAML multi-service functionality by attempting to connect to multiple SPs, using the previously assigned SAML security tokens.
A key advantage of TeraVM is that it can be deployed to cloud services such as Amazon Web Services (AWS), Azure and/or OpenStack; allowing the enterprise to validate access privileges, performance of throughput and latency of core IdP and SP SAML solutions in the cloud.
Click here to download our TeraVM SAML overview.
About TeraVM
VIAVI TeraVM is an application emulation and security performance solution, delivering comprehensive test coverage for application services, wired and wireless networks.
TeraVM is offered as a virtualised solution enabling the flexibility to run anywhere – lab, datacentre and the cloud, with consistent performance coverage, ensuring that highly optimised networks and services can be delivered with minimal risk.
For a demonstration of TeraVM capabilities or for any general queries, please contact us by clicking on the button below.


