Getting the Right Data to Solve IT Chaos
The impact of IoT, hybrid IT and decentralized networks is dominating conversations and column inches. Topics range from how to manage and investigate security and performance issues to the effect on user experience and interaction. In response, vendors and analysts have muddied the waters with phrases such as artificial intelligence and predictive analytics, rather than focusing practical solutions on the network and security managers, engineers, and architects in the trenches.
Regardless of application and infrastructure complexities, with all the network, machine, and cloud data available, the last thing engineers need are more new technologies. They are already overwhelmed by seemingly unrelated and conflicting data points. Energy is better spent making skillful use of existing data sets and ensuring the insight is usable by every IT team.
It’s the Data, Stupid!
Considering the types of network and security intelligence that can be derived from flow, infrastructure data from logs and SNMP polling, or wire data, how many vendors take advantage of all these sources?
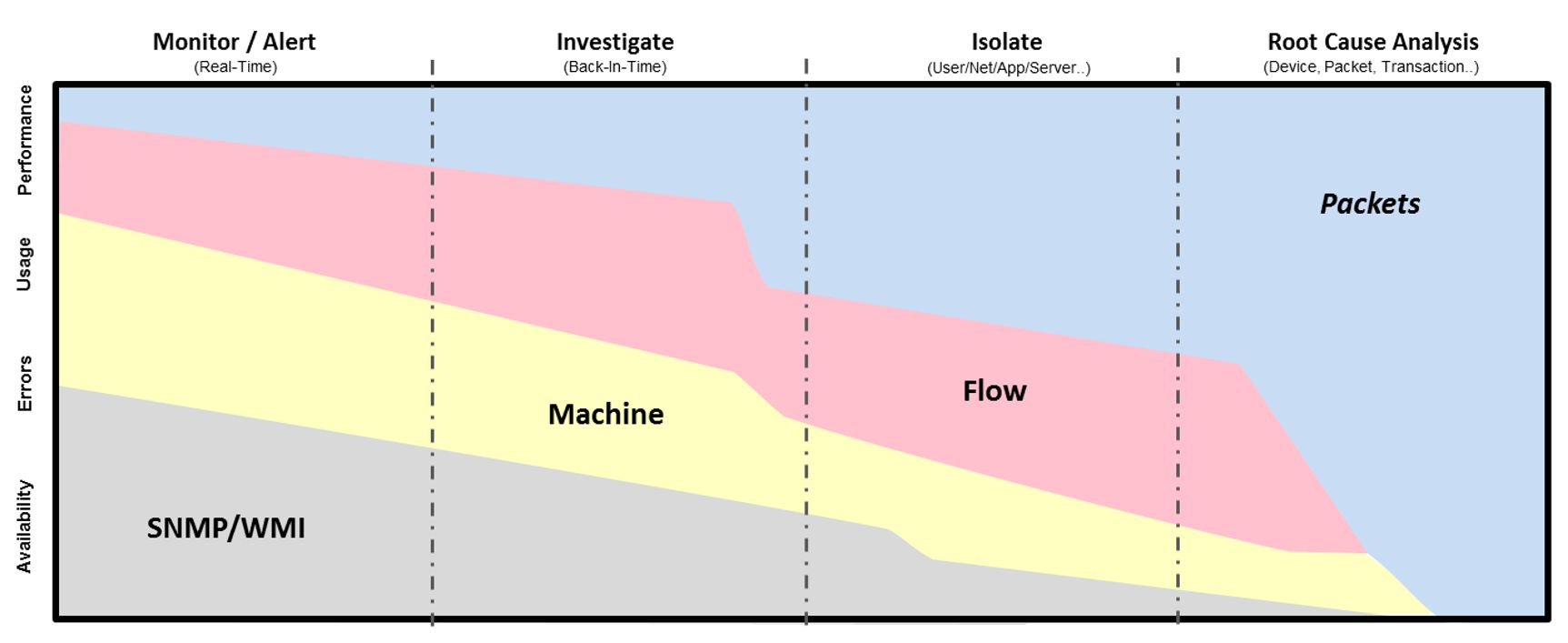
Akin to making decisions without all the facts, network and security tools often collect and report on one or two of these data sets. As a result, most solutions can be classified into one of four categories: SNMP/WMI, Machine, Flow, and Packets.
Reliance on tools generating analysis from limited data sets can lead engineers to draw the wrong conclusions based on partial facts. This impacts a team’s ability to resolve issues. Forrester Research reports that nearly one-third (31 percent) of performance issues take longer than a month or are never resolved. How would drawing insights from all data available, including user-session details, infrastructure, cloud, and application traffic, in an easily-accessible manner change your troubleshooting process?
Losing Track of the User
Another challenge faced by IT teams is understanding how infrastructure is impacting specific end-user experiences. It is difficult to work out exactly what is causing a user to complain when you need to marry AD, IP addresses and MAC information to pinpoint the affected traffic and then work out what is happening. Clarity is further hampered by factors such as remote employees working on multiple devices, the implementation of cloud services, and utilization of SD-WAN. As services traverse multiple abstract environments, IT teams toggle between different metrics and tools to observe performance of diverse resources and then extrapolate user experience.
With incomplete data and end-users using different devices and multiple IPs, it is daunting to determine where to begin troubleshooting to uncover root cause. What if you could begin the troubleshooting process with the one thing that you know for sure – the user’s name?
One Record to Rule Them All
The latest addition to the Observer family, GigaFlow, addresses the challenges of obtaining answers around end-user experience and security quickly from incomplete and disorganized data sets. GigaFlow is a powerful solution that delivers enriched flow records that structure and stitch together user, network, and infrastructure data into a single record. It delivers deep insight providing end-to-end visibility beyond the core to the farthest reaches of the IT network. Fast and effective troubleshooting and forensics investigations are now just a mouse click away.
Enriched flow records provide in-depth details on network device types, connectivity, traffic control, and usage patterns down to the individual user for all communication traversing the environment. GigaFlow employs a user-centric approach for reporting and investigations, automatically calling up complete details about client devices, performance issues, access behavior, and activity from the user’s name. Coupled with Observer Apex and GigaStor, the Observer platform complements the expansive enriched flow insight with in-depth user experience and security forensic details from captured packets.
Learn more about harnessing the power of GigaFlow for security and performance investigations by visiting www.viavisolutions.com/observergigaflow.